Installing and using the Key9 Proxy server for Linux
Scope
This document covers the setup of the Telos Alliance Key9 License Server Proxy for Linux on a computer in your facility. Many Telos products require this for licensing; however, no individual product support is covered in this document.
Description
Some Telos Alliance products require a license to operate. These licenses activate (or deactivate) features allowing flexibility in your operating model and allowing for software updates, priority support, etc. These licenses are controlled by a cloud-located activation server, meaning your products must have access to this server.
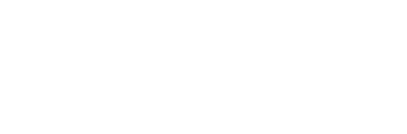
Often the networks to which these products are connected are purposely not connected to the internet. For this reason, Telos Alliance offers this proxy server which can reside on a computer that DOES have access to the internet.
Here's a diagram of a typical configuration.
Configuration
Uninstall any previous version
If you have previously installed this linux verstion you need to stop it and unstall it to prevent any conflicts.
execute the following commands. These commands do not remove the file. it stops the service and removes the service so it does not run.
$ ./key9proxy --stop
$ .key9proxy --uninstall
sudo command ahead of any other commands.The
sudo command in Linux is used to execute commands with elevated privileges or as a different user, typically the superuser (root). The word "sudo" stands for "superuser do." When you prefix a command with sudo and enter your password, it allows you to perform administrative tasks that require higher privileges than your current user account provides.- Click here to download the Key9 Proxy and save it. If you are in a Linux terminal interface using a
wgetcommand, you can use;wget https://telos-public.s3.amazonaws.com/downloads/telos/Key9Proxy/linux/key9proxy2.0.1
- Ensure the file is executable by using the command
$ chmod +x key9proxy2.0.1
- Create a configuration file.
$ ./key9proxy2.0.1 --config
To continue, you must type YES to agree to the EULA (End User License Agreement).- Specify the Listen Interface and port. The default is [0.0.0.0:42131] which means listening for license requests on any network interface. Press Enter to accept the default.
- Specify the server address. you must specify either secure2.telos-systems.com:42131 or https://secure2.telos-systems.com depending on which you prefer.
- the latter (https) uses secure http on port 443 to communicate with the license server. the fist metod connects to the server on port 42131. https may be easier for firewalls to handle.
- Setup the HTTP server.
- Run the proxy in test mode.
$ ./key9proxy --test
You will see the message;
Telos Alliance License Server Proxy v1.0.3. Copyright (C) 2023 TLS Corp.
-------------------------------------------------------------------------
I: 16:27:02 Started on linux-systemd
I: 16:27:02 Waiting client connections on 0.0.0.0:42131...
- Press Control+C to exit.
- Install as a service so the proxy server starts when the system is rebooted.
$ ./key9proxy --install
- Start the service
$ ./key9proxy --start
For the run service as user question, you may press enter and leave the value blank or you may enter the name of the user that the service will run as.
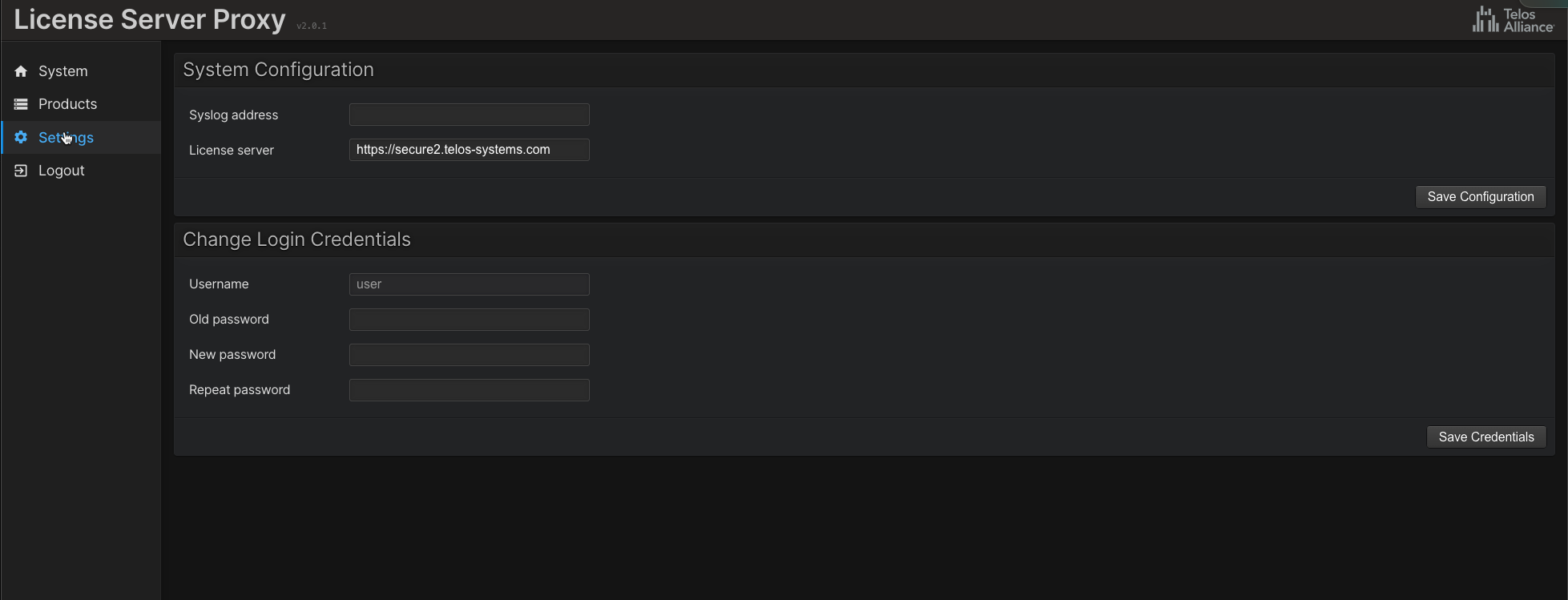
HTTP interface
open a browser and navigate to the pc where the proxy server is running on the port you specified durring config. In out example port 8080 so292.168.2.120:8080
After you agree to the EULA and configure a login, you can manage the server from this page.
Note that eh Products will only be populated by Products that support this feature yet. as of this writing It is believed only Zephyr Connect and a couple of other specialized products like AAR support it. more will be added.
Notes
After the proxy server is installed, configured, and tested, you need to configure all telos alliance products to point to the proxy server instead of the cloud license server.
The product configuration depends on the product. For example, VXs does this through an unlinked web page.
If you modify the configuration file, you must restart the service before the new options take effect.
When configuring the service, you may leave the username blank.
It is safe to briefly take the proxy server down even if the products use it. The license refresh mechanism will retry later.
key9proxy offers additional command line options. Executing the program without arguments will display help texts with the available options.
Troubleshooting
- Use ping to see if the cloud license server responds. The primary cloud server address is secure2.telos-systems.com.
- Use traceroute to determine if the server is reachable.
- Use telnet to find out if a TCP connection may be established on the license server on the proxy server:
telnet <ip-address> <port>where <ip-address> is the address of the machine and <port> is usually 42131. For example, telnet to 192.168.2.224:42131 should allow you to connect.
When a firewall is present, the only requirement is to allow outgoing TCP connections to secure2.telos-systems.com on port 42131. There is no need to open incoming ports since the products and the proxy always reach outward to the license server. The license server will never make an inbound connection. While most firewalls allow outgoing connections by default, for some customers, this has to be explicitly allowed.